HTTP vs HTTPS: Why Your Website Security Matters
HTTP and HTTPS aren't just technical jargon — the difference affects your SEO rankings, visitor trust, and whether browsers actively warn people away from your site. Here's everything you need to know.
The Small Letter That Makes a Big Difference
Look at the address bar in your browser right now. See how the URL starts with "https://" rather than "http://"? That extra "s" represents one of the most important security decisions a website owner can make — and one that affects not just security, but SEO, user trust, and whether modern browsers actively try to drive visitors away from your site.
Most people know vaguely that HTTPS is "more secure" than HTTP. Far fewer understand why, what specifically it protects against, and why Google has spent years turning HTTPS into a de facto requirement for anything on the web. This guide covers all of it: what each protocol actually does, the difference between them, what happens when you don't have HTTPS, and how to get it right.
What HTTP Actually Is
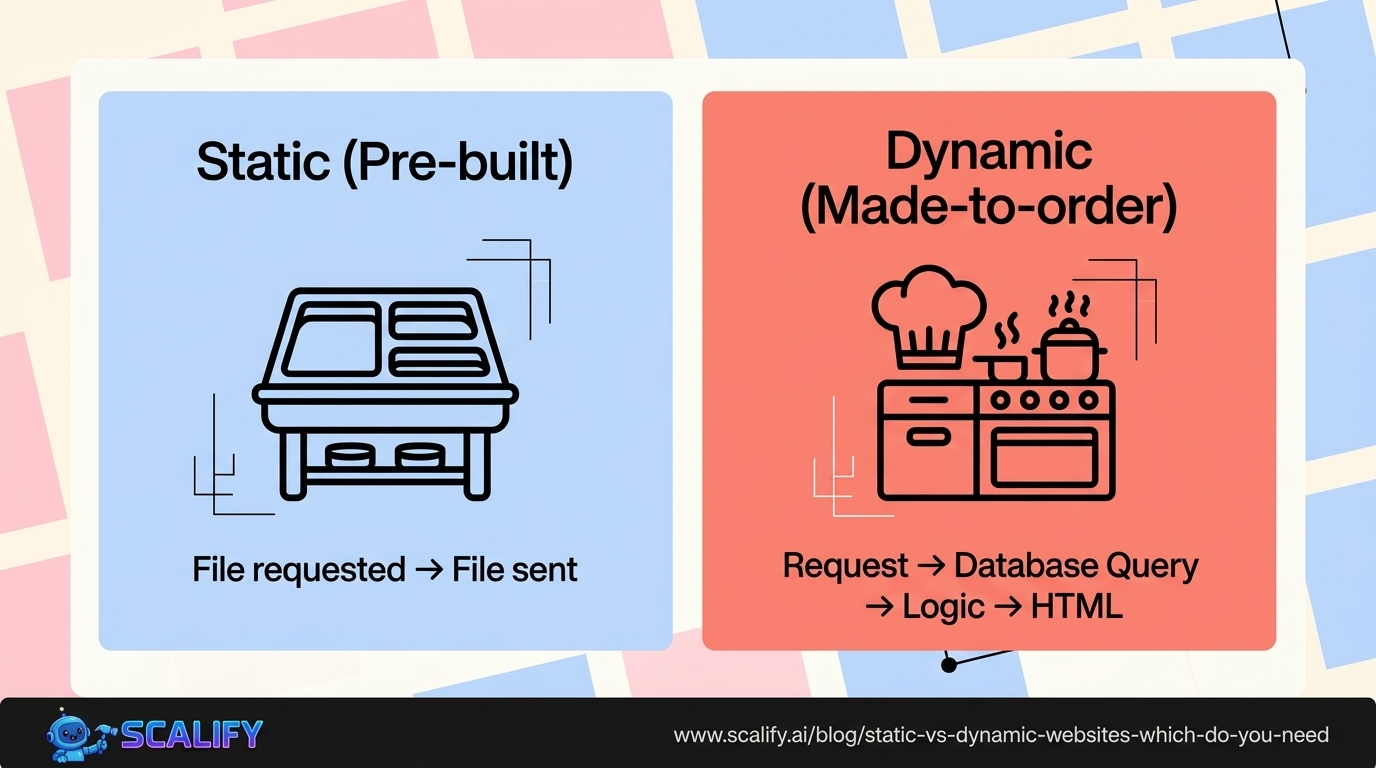
HTTP stands for HyperText Transfer Protocol. It's the foundational protocol of the World Wide Web — the set of rules that governs how data is requested and transmitted between web browsers and web servers.
When you type a URL into your browser, your browser sends an HTTP request to the server where the website lives. The server processes that request and sends back an HTTP response containing the page's content. This request-response cycle happens thousands of times per second across the internet, and HTTP is the language both sides use to communicate.
HTTP was designed in the early 1990s for a simpler, more innocent internet. The original purpose was sharing academic documents. Security wasn't a primary design concern — the protocol transmits data in plain text, meaning everything that flows between a browser and server is readable by anyone who can intercept it.
In the early days of the web, when most sites were simply displaying static information and very little personal or financial data was being transmitted online, this was acceptable. As the web evolved into a platform for banking, shopping, healthcare, communication, and every other domain of human activity, it became a serious problem.
What HTTPS Is and How It's Different
HTTPS stands for HyperText Transfer Protocol Secure. It's HTTP with an encryption layer added on top.
That encryption layer is provided by TLS (Transport Layer Security), previously known as SSL (Secure Sockets Layer). You'll still hear people say "SSL certificate" to refer to the certificate that enables HTTPS, even though TLS is the current standard — the terminology has just stuck.
The fundamental difference is this: HTTP transmits data as plain text. HTTPS encrypts data before transmitting it. Anyone who intercepts the data stream gets scrambled gibberish instead of readable content.
Let's be specific about what that means in practice.
On an HTTP site, if you fill out a login form and submit your password, that password travels from your browser to the server as readable text. If anyone is monitoring the network traffic between you and the server — on a public WiFi network, for instance, or anywhere along the chain of internet infrastructure the data passes through — they can read your password. Verbatim.
On an HTTPS site, that password is encrypted before it leaves your browser. What travels across the network is an indecipherable encrypted string. Even if someone intercepts it, they can't read it. The server has the cryptographic key needed to decrypt it; no one else does.
How TLS Encryption Actually Works
The encryption process behind HTTPS is worth understanding at a conceptual level, because it's more clever than just "scrambling the data."
When your browser connects to an HTTPS site, the two sides go through what's called a TLS handshake. During this handshake, they accomplish several things:
Authentication. The server presents its TLS certificate — a digital credential issued by a trusted Certificate Authority (CA). This certificate contains the server's public key and a cryptographic signature from the CA confirming: "We have verified that this certificate belongs to who it claims to belong to." Your browser checks this certificate against its built-in list of trusted CAs. If it verifies, you know you're actually talking to the legitimate server, not an impostor.
Key exchange. The browser and server use asymmetric encryption (public/private key cryptography) to securely negotiate a shared session key. The public key can be shared with anyone; data encrypted with it can only be decrypted with the corresponding private key, which the server holds securely.
Session establishment. Once the shared session key is established, both sides switch to symmetric encryption for the actual data transfer — symmetric encryption is computationally faster and more efficient for large amounts of data. This session key is unique to this connection and this session. Even if an attacker records all the traffic, they can't decrypt it without the session key.
The practical result: not only is the data encrypted, but both sides have verified they're talking to who they think they're talking to. Man-in-the-middle attacks — where an attacker positions themselves between browser and server to intercept and potentially modify traffic — are prevented by the authentication step. An attacker can't present a fraudulent certificate that your browser trusts without having compromised a Certificate Authority, which is an extremely high bar.
What HTTPS Protects Against
Understanding the specific threat categories HTTPS defends against helps clarify why it matters for different types of sites and users.
Eavesdropping
The most obvious threat: someone intercepting and reading data in transit. This is trivially easy on unencrypted public WiFi networks — any device on the same network can be configured to capture traffic. HTTPS makes intercepted data unreadable.
Data Tampering
HTTP connections can be modified in transit — an ISP, a network operator, or a man-in-the-middle can inject content into HTTP pages. This has been used to inject ads into web pages, to add malware to downloaded software, and to modify the content of news articles. HTTPS prevents this because any modification to encrypted data produces gibberish when decrypted; tampering is detectable and rejected.
Session Hijacking
When you log into a website, your session is typically tracked by a cookie. On HTTP, this cookie travels in plain text and can be captured by anyone watching the network. With your session cookie, an attacker can impersonate you to the website — taking over your account without knowing your password. HTTPS keeps cookies encrypted in transit.
Content Injection and Malvertising
ISPs and other network intermediaries have been caught injecting advertising into HTTP web pages — modifying the content of a page you're viewing to add ads that the website owner didn't place there. HTTPS prevents this by making the page content cryptographically verified and tamper-evident.
HTTPS and SEO: A Direct Ranking Factor
If the security arguments weren't enough, Google made HTTPS a direct ranking factor in 2014. Sites with HTTPS get a ranking boost in search results compared to equivalent HTTP sites.
The signal isn't enormous on its own — Google has described it as a "tiebreaker" and a lightweight factor compared to content quality and backlinks. But in competitive search landscapes where the difference between ranking positions can come down to many small factors, it's a free win you'd be foolish to leave unclaimed.
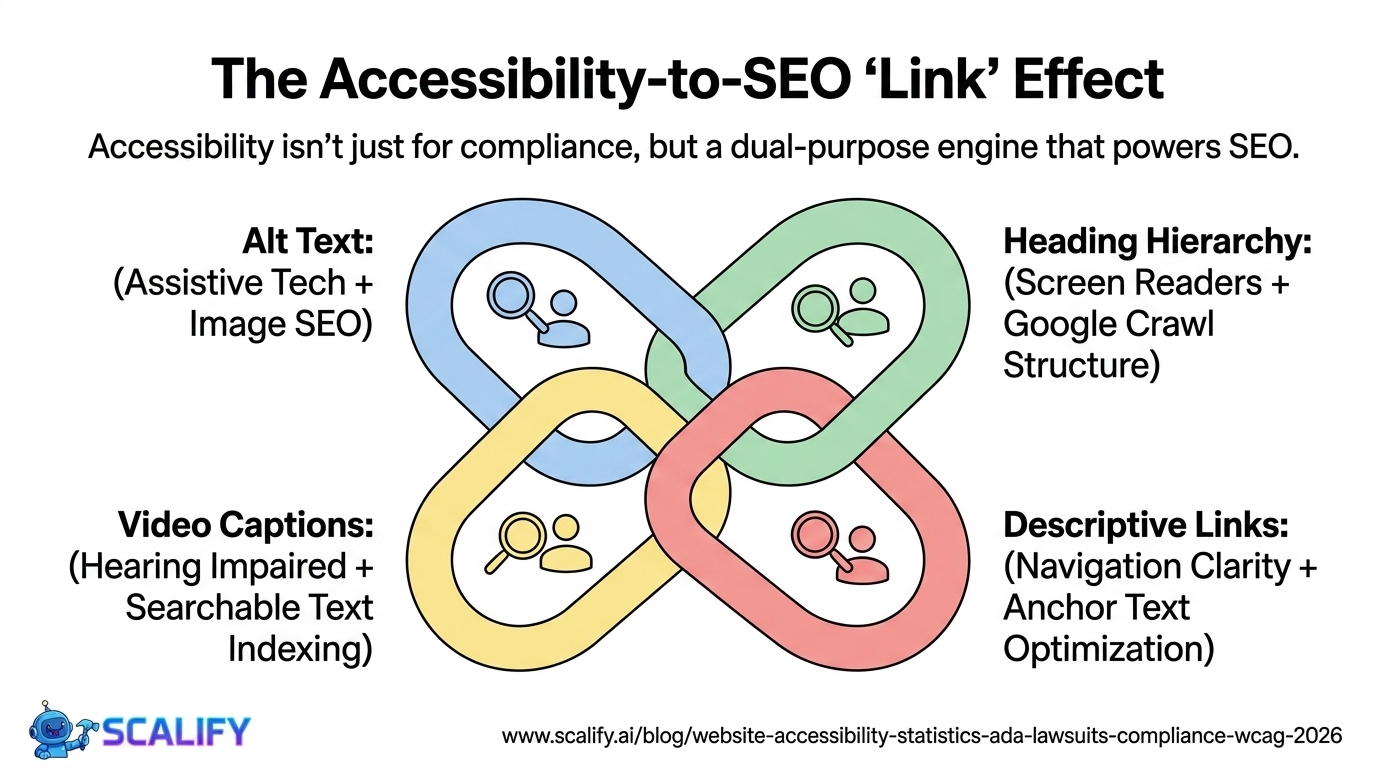
Beyond the direct ranking signal, there are indirect SEO impacts. Users who land on an HTTP site and see a "Not Secure" warning from their browser may immediately hit back — increasing your bounce rate, which sends a negative engagement signal. A site that users avoid doesn't accumulate the behavioral signals that support ranking.
Google's Search Console also treats HTTP and HTTPS as separate sites. If you have inbound links pointing to both http://yoursite.com and https://yoursite.com without proper redirects, you're splitting your link equity. HTTPS implementation needs to be done correctly — with proper 301 redirects from HTTP to HTTPS, HSTS headers, and canonical tags — to fully consolidate that equity.
Browser Warnings: How Not Having HTTPS Hurts You
Google Chrome, which accounts for roughly 65% of browser market share globally, has been aggressively flagging HTTP sites for years. The progression has been deliberate and escalating:
In 2017, Chrome began showing a "Not Secure" label in the address bar for HTTP pages that contain password fields or credit card inputs. Even if your site didn't ask for passwords, the message was clear: HTTPS is the standard, HTTP is not.
In 2018, Chrome expanded the "Not Secure" label to all HTTP pages. Not just forms. All HTTP pages, all the time. If your site doesn't have HTTPS, every Chrome user who visits sees "Not Secure" in the address bar.
For some categories of content — HTTP pages with form submissions — Chrome shows a full interstitial warning page, similar to the warnings shown for malware. Your visitor sees a red warning screen and has to choose to proceed anyway. Most don't.
Firefox and Safari have implemented similar warnings. The browser ecosystem has collectively decided that HTTPS is the baseline, and they're making HTTP increasingly uncomfortable for visitors — which directly impacts your bounce rate, trust, and conversions.
A business website with a "Not Secure" label is actively being sabotaged by the browser before the visitor has seen a single word of your content. There is no good reason to be in this position in 2026.
Types of TLS Certificates
Not all SSL/TLS certificates are the same. There are three main types, with different validation levels and different appropriate use cases.
Domain Validation (DV) Certificates
DV certificates verify only that the certificate applicant controls the domain. The Certificate Authority checks that you can respond to email sent to an admin address at the domain, or that you can place a specific file on the web server. No verification of who the organization is, what they do, or whether the business is legitimate.
DV certificates are the most common, the fastest to obtain (often issued in minutes), and the cheapest (many are free through Let's Encrypt). They provide full encryption — the padlock in your browser's address bar doesn't indicate more or less encryption based on certificate type — but they provide minimal identity assurance. A phishing site impersonating your bank can get a DV certificate just as easily as your bank can.
For most small business websites and blogs, a DV certificate is perfectly appropriate. You get full encryption, the browser padlock, and no cost.
Organization Validation (OV) Certificates
OV certificates require the Certificate Authority to verify that the certificate applicant is a legitimate, legally registered organization. The CA checks business registration records, confirms the organization's address, and verifies that the person requesting the certificate is authorized to do so on behalf of the organization.
This provides more assurance about who is behind the website, not just that the traffic is encrypted. Visitors who dig into the certificate details can see the verified organization name. OV certificates cost $50–300/year and take hours to days to issue.
OV certificates are appropriate for organizational and governmental websites where institutional identity assurance matters beyond just encryption.
Extended Validation (EV) Certificates
EV certificates require the most rigorous identity verification — thorough checks of legal existence, physical address, operational status, and authorization. They take the longest to obtain and cost the most.
EV certificates historically triggered a green address bar and displayed the organization name prominently in the browser. Chrome and other browsers removed this special green bar treatment in 2019, concluding that users weren't meaningfully distinguishing between certificate types. The enhanced visual trust indicator no longer exists in most browsers, which has significantly reduced the value proposition of EV certificates for most organizations.
Some high-security banking and financial sites still use EV certificates for the organizational validation record they provide, but they're no longer meaningfully differentiated in typical user experience.
How to Get HTTPS: The Practical Path
Getting HTTPS on your website is easier than it's ever been. Here's what the path looks like.
For Websites on Managed Platforms
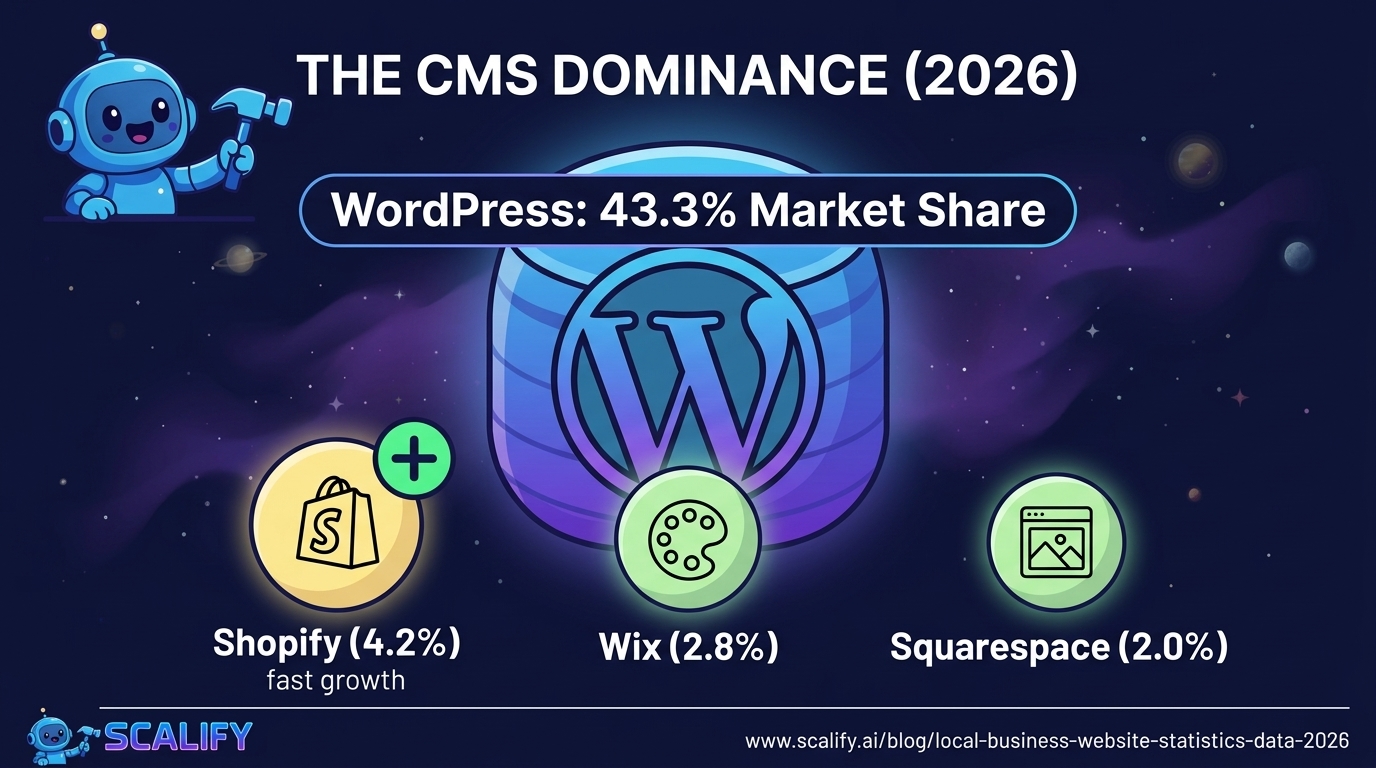
If your site is on Webflow, Shopify, Squarespace, Wix, or a similar managed platform, HTTPS is almost certainly already handled automatically. These platforms provision and renew SSL certificates for all sites on their infrastructure without any action from you. If you have a custom domain connected, the certificate covers that domain. Check your domain settings to confirm HTTPS is active — it should be on by default.
For WordPress on Managed Hosting
Quality managed WordPress hosts (WP Engine, Kinsta, SiteGround, Bluehost) also provision SSL certificates automatically, often using Let's Encrypt. Log into your hosting control panel and look for SSL settings — there's usually a one-click "enable SSL" option. Many hosts have already done this by default for all hosted sites.
For Custom Server Setups
If you're managing your own server, Let's Encrypt is the answer. Let's Encrypt is a free, automated Certificate Authority that makes HTTPS accessible to everyone. The Certbot tool (certbot.eff.org) automates the process of obtaining, installing, and renewing Let's Encrypt certificates on most Linux web servers. For a properly configured server, getting HTTPS with Let's Encrypt takes under 10 minutes and the certificate renews automatically every 90 days.
The Critical Step: Proper Redirects
Getting a certificate installed is only half the job. You also need to ensure all HTTP traffic redirects to HTTPS. Without this, visitors who type your domain without "https://" or follow an old HTTP link get the unencrypted version. More importantly, search engines see HTTP and HTTPS as different sites, and without redirects, your SEO equity is split.
Configure a server-level 301 redirect from http://yourdomain.com to https://yourdomain.com. This should be set up for both the www and non-www versions of your domain. Your hosting platform or control panel usually has settings for this, or it can be configured in your server's config files.
HSTS: The Extra Layer
HSTS (HTTP Strict Transport Security) is an optional but recommended security header that tells browsers: "This site only works over HTTPS. Never try to connect over HTTP, even if someone types the URL without https://." Once a browser has seen this header for your site, it will always use HTTPS for future connections — even if the user types just the domain name — removing the window of vulnerability during the initial redirect.
Common HTTPS Mistakes
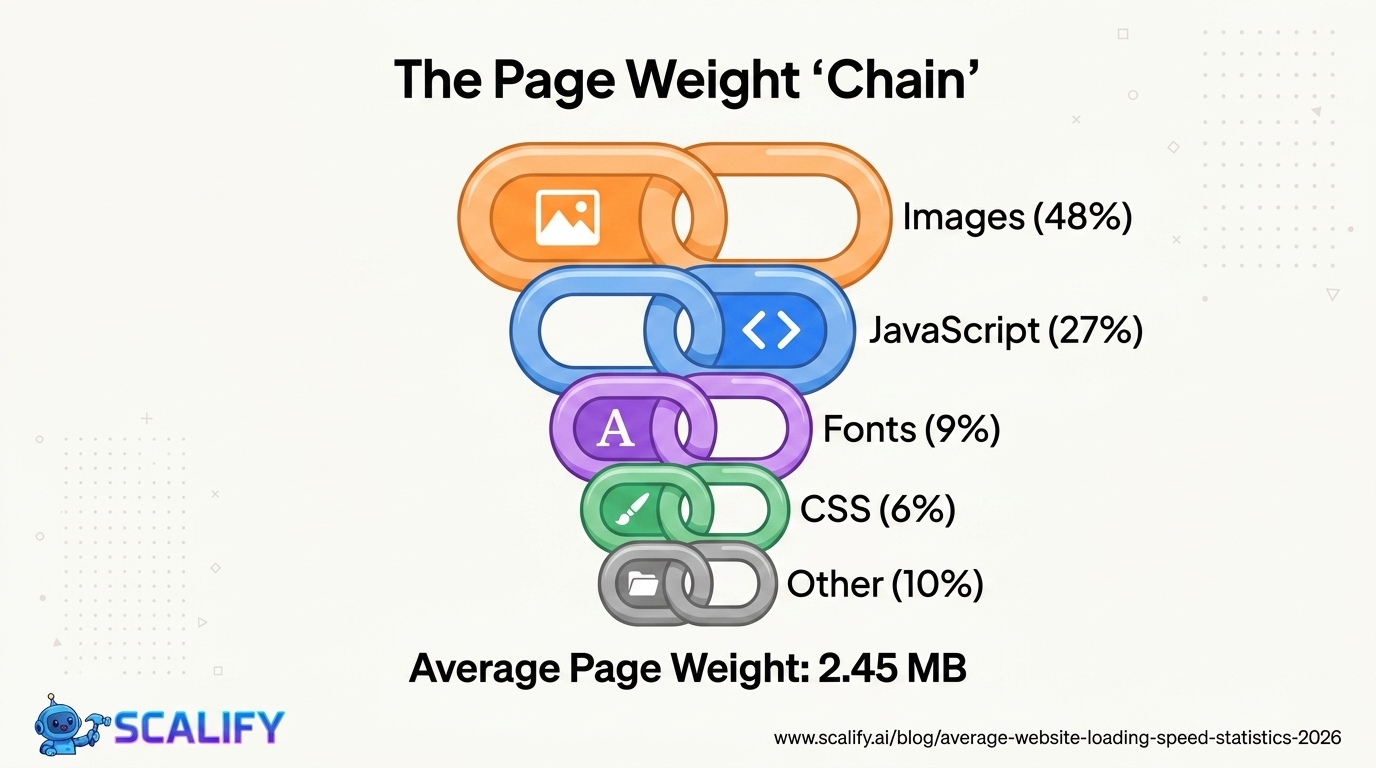
Mixed content. A page served over HTTPS that loads resources (images, scripts, stylesheets) over HTTP has "mixed content." Browsers will either block the insecure resources or display a warning. When you migrate a site to HTTPS, you need to update all internal links and resource URLs to use HTTPS, not just the page URLs themselves. Missing even one HTTP resource can trigger browser warnings.
Certificate expiration. TLS certificates have expiration dates. When a certificate expires, browsers show a full security warning to visitors — similar to the red malware warnings — until the certificate is renewed. Most certificate providers offer automatic renewal; make sure it's configured and that the email for renewal notifications is actively monitored.
Self-signed certificates. Generating your own certificate without using a trusted Certificate Authority results in browser warnings because the cert isn't from a recognized authority. Self-signed certs are fine for internal testing but must never be used on public-facing sites. Use Let's Encrypt instead — it's free and properly trusted.
Not updating internal links after migration. When you migrate from HTTP to HTTPS, search engine crawlers need to be told about the change. Update your sitemap, submit it to Google Search Console, and verify your HTTPS site in Search Console. Also update any Google Analytics, Google Ads, or other marketing tool integrations to reflect the HTTPS URLs.
The Bottom Line
HTTPS is not optional anymore. It hasn't been since at least 2018, when Chrome started warning users about every HTTP site by default. It's a baseline requirement for visitor trust, browser compatibility, SEO, and basic security hygiene. The barriers to having it are lower than ever — free certificates, one-click installation on most hosts, automatic renewal.
If your site is still on HTTP, fix it today. If you're building a new site, start with HTTPS configured correctly from the beginning. It's not a technical upgrade to defer — it's a fundamental that should be on by default for anything on the public web.
When you build with Scalify, HTTPS is handled correctly from day one — part of the foundation of every site we deliver, along with the performance, security, and technical quality that make a website actually work for your business.







.jpeg)
.jpeg)