SSL Certificates Explained: What They Are and Why You Need One
SSL certificates are what put the 'S' in HTTPS — and without one, browsers actively warn visitors your site isn't safe. Here's exactly what they are, how they work, and how to get one.
The Padlock That Visitors Trust and Google Rewards
Look at your browser's address bar right now. If you're on a properly secured website, you'll see a padlock icon before the URL, and the address starts with "https://" rather than "http://". That padlock and that "s" both exist because of an SSL certificate — a digital credential installed on the web server that enables encrypted, authenticated communication between the server and every visitor's browser.
Most website owners know they need one. Fewer understand what it actually does, why the different types exist, or what the practical consequences are of not having one installed correctly. This guide covers all of it — what SSL certificates are, how they work, what the different types mean, how to get one, and the mistakes to avoid.
What an SSL Certificate Actually Is
An SSL certificate is a small digital file installed on a web server that serves two distinct purposes: it enables encryption of data in transit, and it provides authentication — proof that the server is actually operated by who it claims to be.
The certificate contains several pieces of information: the domain name it's issued for, the organization it's issued to (for higher-validation certificates), the Certificate Authority (CA) that issued it, the date it was issued, the date it expires, and the public key that's used in the encryption process.
When your browser connects to an HTTPS site, the server presents this certificate. Your browser checks it against its built-in list of trusted Certificate Authorities. If the certificate is valid, hasn't expired, is from a trusted CA, and matches the domain you're connecting to, the browser proceeds with establishing an encrypted connection. If any of these checks fail, the browser shows a security warning.
A quick note on terminology: SSL (Secure Sockets Layer) is the older protocol that's been deprecated and replaced by TLS (Transport Layer Security). Modern certificates use TLS. However, the industry still uses "SSL certificate" as the common term because the name stuck even after the underlying technology was updated. When someone says "SSL certificate" in 2026, they mean a TLS certificate. The padlock in your browser is a TLS connection. The names are used interchangeably.
How Encryption Works: The Non-Technical Version
Here's the core mechanism behind what SSL/TLS actually does, explained without getting lost in cryptography.
Without encryption, data traveling between your browser and a web server moves as plain text. If you type your password into a login form on an unencrypted site and submit it, that password travels across the network as readable characters. Anyone positioned to intercept that network traffic — someone on the same public WiFi network, a malicious actor at any point along the route, or your ISP — can read it verbatim.
With encryption, the data is transformed into an unintelligible scramble before it leaves your browser. The server holds the key needed to decrypt it. Anyone who intercepts the data in transit gets a string of gibberish that's computationally infeasible to crack with current technology.
The mechanism works through asymmetric encryption during setup (a public key visible to everyone, a private key held only by the server) to securely establish a shared session key, then switches to symmetric encryption for the actual data transfer (faster and more efficient for bulk data). This combination — asymmetric for the handshake, symmetric for the session — is what makes HTTPS both secure and performant.
The authentication piece is equally important. Without it, encryption alone wouldn't prevent a "man-in-the-middle" attack — where an attacker positions themselves between you and the legitimate server, decrypts your traffic, reads or modifies it, and re-encrypts it before passing it on. Certificate authentication prevents this by proving the server is who it claims to be: a certificate is only valid if it's been issued by a trusted CA to the entity that actually owns the domain.
The Three Types of SSL Certificates
Not all SSL certificates are the same. They differ in how much identity verification the Certificate Authority performs before issuing them — which has practical implications for what they prove about the site and who should use each type.
Domain Validation (DV) Certificates
Domain Validation certificates are the most common and the fastest to obtain. The only thing the Certificate Authority verifies is that the person requesting the certificate controls the domain — typically by requiring the applicant to place a specific file on the web server or respond to an email sent to an admin address at the domain.
DV certificates can be issued in minutes. Many are available for free through Let's Encrypt (more on this shortly). They provide full encryption — the padlock appears in the browser, and data is protected just as effectively as with more expensive certificate types.
What DV certificates don't verify: who actually operates the site. A phishing site designed to impersonate a bank can obtain a DV certificate for its lookalike domain just as easily as the real bank. The padlock tells you that your connection to that server is encrypted — it doesn't tell you whether that server is trustworthy.
DV certificates are appropriate for: most small business websites, blogs, personal sites, and any site where the encryption benefit matters but organizational identity verification isn't critical. This covers the vast majority of websites.
Organization Validation (OV) Certificates
Organization Validation certificates require the Certificate Authority to verify not just domain control but the legitimacy of the organization requesting the certificate. The CA checks business registration records, confirms the organization's address exists, and verifies that the person requesting the certificate is authorized to act on the organization's behalf.
OV certificates take longer — hours to a few days for the verification process — and cost more than DV certificates, typically $50–300 per year. Visitors who examine the certificate details can see the verified organization name, providing an additional layer of identity assurance.
OV certificates are appropriate for: business and organizational websites where institutional identity verification provides meaningful reassurance to visitors. Government sites, healthcare organizations, and businesses in sectors where trust and legitimacy carry extra weight.
Extended Validation (EV) Certificates
Extended Validation certificates require the most rigorous verification process. CAs conduct thorough checks of legal existence, physical address, operational status, jurisdiction, and authorization. The process takes days to complete and EV certificates are the most expensive, often $200–500+ per year.
Historically, EV certificates triggered a green address bar in browsers and displayed the organization name prominently next to the padlock — a strong visual trust signal. Chrome removed this visual distinction in 2019, followed by other major browsers, concluding that users weren't meaningfully interpreting the difference and that the enhanced display was creating false confidence. Today, there's no visible difference to typical visitors between a DV and an EV certificate.
The primary remaining value of EV certificates: the organizational verification record they create and the audit trail for highly regulated industries. Most businesses can achieve equivalent user trust signals through DV or OV certificates and other on-site trust elements (testimonials, reviews, clear contact information).
Single Domain vs. Wildcard vs. Multi-Domain Certificates
Beyond validation levels, SSL certificates also differ in how many domains or subdomains they cover.
Single domain certificates cover one specific domain — either yoursite.com or www.yoursite.com, not both (though most modern certificates cover both the root and www automatically). For simple single-domain websites, this is all you need.
Wildcard certificates cover a domain and all its subdomains at one level. A wildcard certificate for *.yoursite.com covers www.yoursite.com, blog.yoursite.com, shop.yoursite.com, app.yoursite.com, and any other subdomain at that level. If you run multiple services under different subdomains, a wildcard certificate is more economical than purchasing individual certificates for each.
Multi-domain (SAN) certificates cover multiple distinct domains — yoursite.com, yourothersite.com, yourbrand.net — under a single certificate. Useful for businesses operating multiple domains that they want to manage together. Also called Subject Alternative Name (SAN) certificates because they use the SAN field in the certificate to list multiple domains.
Certificate Authorities: Who Issues These?
Certificate Authorities are organizations trusted to verify identities and issue certificates. Browsers maintain a list of trusted CAs built into the browser software — if a certificate is issued by a CA on that list, the browser trusts it. If it's issued by an entity not on the list (or self-signed by you), the browser shows a warning.
The major commercial CAs include DigiCert, Sectigo (formerly Comodo), GlobalSign, and Entrust. These are the traditional providers that have been in the business for decades and offer certificates across all validation levels.
Let's Encrypt changed the landscape dramatically when it launched in 2016. Let's Encrypt is a free, automated, open Certificate Authority backed by major tech companies including Mozilla, Google, and Cisco. It issues DV certificates for free, automatically, and with automated renewal — removing cost and complexity from the process of getting HTTPS.
Let's Encrypt has been transformative for the web. Before it, small websites and developers who couldn't afford commercial certificates often ran on HTTP because getting a certificate required cost and technical effort. After Let's Encrypt, there's genuinely no barrier. The adoption of HTTPS across the web accelerated dramatically after its launch, and today most web hosting platforms use Let's Encrypt certificates automatically.
How to Get an SSL Certificate
The path to getting an SSL certificate depends on your setup:
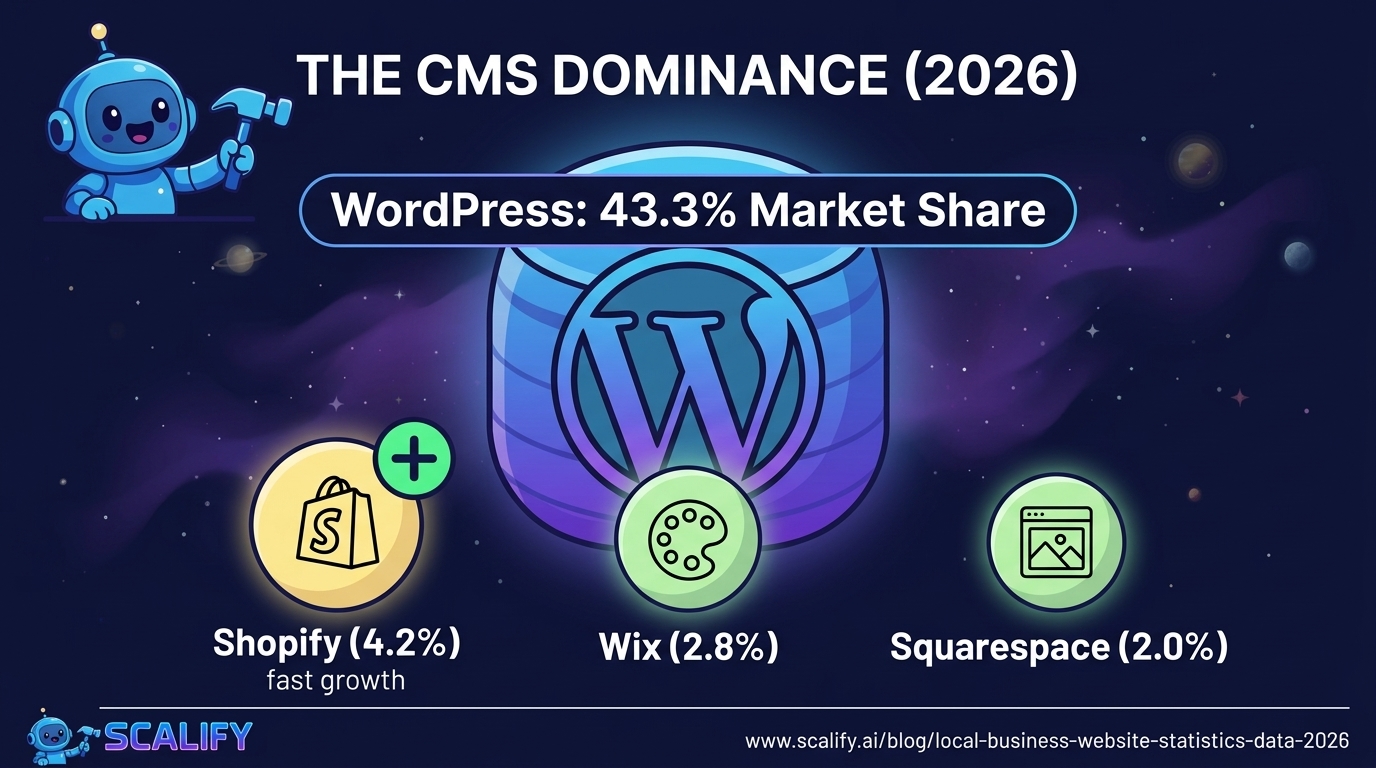
Managed Platform (Webflow, Shopify, Squarespace, Wix)
If your site is hosted on a managed platform, SSL is handled automatically. These platforms provision and renew Let's Encrypt certificates for all custom domains connected to their infrastructure. You typically don't need to do anything beyond connecting your custom domain — HTTPS is on by default.
Verify by checking your domain settings in the platform dashboard. There should be a green checkmark or "SSL Active" indicator next to your domain. If it's not active, most platforms have a one-click "Enable SSL" option or will provision the certificate within a few hours of domain connection.
Managed WordPress Hosting (WP Engine, Kinsta, SiteGround)
Quality managed WordPress hosts include automatic SSL certificate provisioning. Log into your hosting control panel, navigate to SSL or HTTPS settings, and either confirm it's already active or enable it with one click. The underlying certificate is typically Let's Encrypt, renewed automatically every 90 days without any action required from you.
Traditional cPanel Hosting
Most cPanel hosting setups include AutoSSL, which automatically provisions and renews Let's Encrypt certificates for all hosted domains. Log into cPanel, navigate to the SSL/TLS section, and look for AutoSSL status. If it's running and showing green checkmarks for your domains, you're covered.
If your host doesn't offer AutoSSL, you can install a Let's Encrypt certificate manually using Certbot — the official Let's Encrypt client. Installation instructions are well-documented for Apache, Nginx, and other web servers at certbot.eff.org.
Custom Server
On a self-managed server, Certbot is the standard path. Install Certbot on your server, run it with the appropriate plugin for your web server software (Apache or Nginx), and it handles certificate issuance and automatic renewal. The process typically takes under 10 minutes for someone comfortable with command-line tools.
Commercial Certificate Purchase
If you need an OV or EV certificate, or a wildcard/multi-domain certificate that Let's Encrypt doesn't support in the configuration you need, you'll purchase from a commercial CA. The process involves generating a Certificate Signing Request (CSR) on your server, submitting it to the CA along with verification documentation, receiving the issued certificate, and installing it on your server. Most commercial CAs provide step-by-step instructions for each server type.
Installing SSL Correctly: The Steps Beyond the Certificate
Getting a certificate installed is necessary but not sufficient. Proper HTTPS implementation requires a few additional steps:
Redirect HTTP to HTTPS. With a certificate installed, both http:// and https:// versions of your URLs may be accessible. Without a redirect, visitors who type your domain without "https://" get the unencrypted version. You need a server-level 301 redirect from all HTTP URLs to their HTTPS equivalents. In cPanel, this is often a checkbox. In Nginx or Apache, it's a configuration block. Your hosting platform may have this as a toggle.
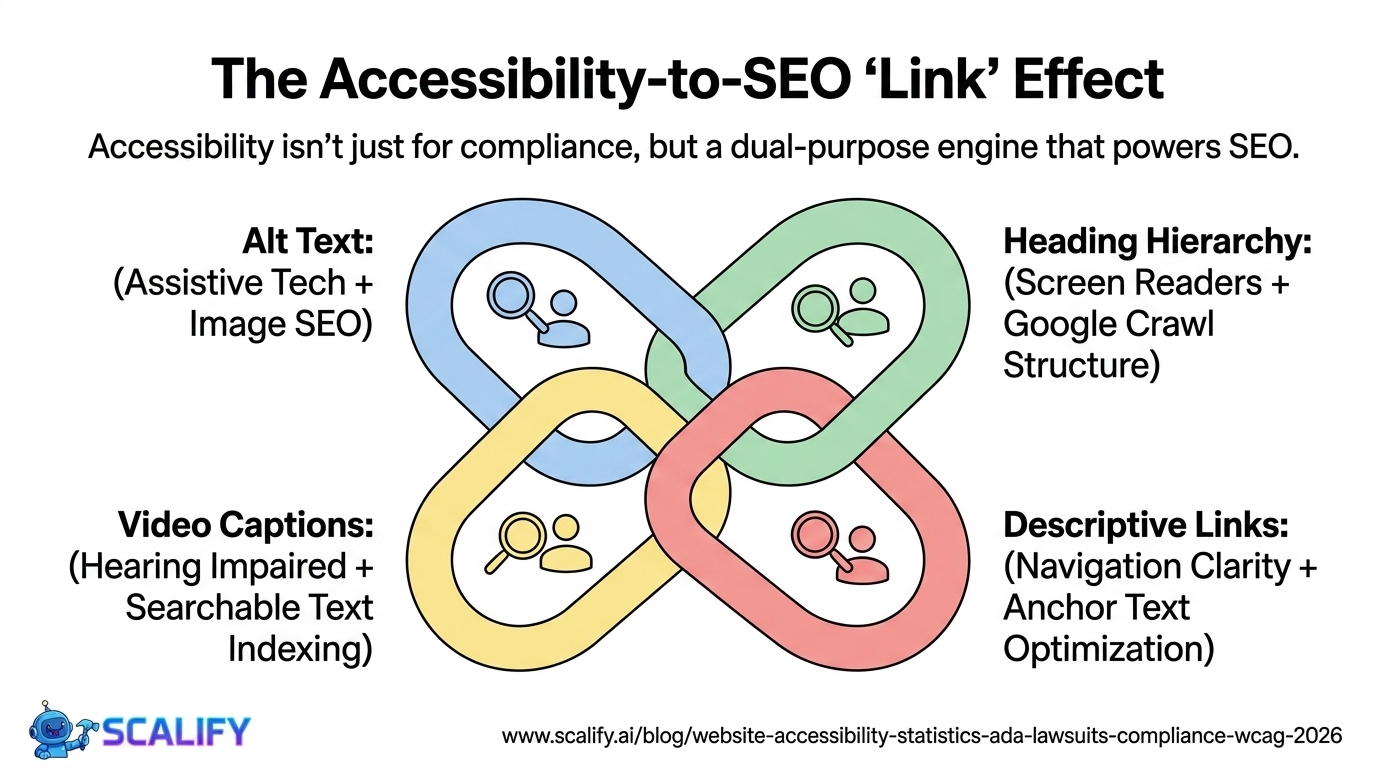
Fix mixed content. If your HTTPS page loads any resource (image, script, stylesheet, iframe) over HTTP, you have mixed content. Browsers either block the insecure resource entirely (showing a broken image or broken functionality) or display a "Not Fully Secure" warning instead of the padlock. After migrating to HTTPS, audit all resource URLs in your HTML, CSS, and JavaScript and update any HTTP references to HTTPS.
Update internal links. Any internal links using absolute URLs (https:// rather than relative paths) need to be updated from http:// to https://. For WordPress, the Velvet Blues Update URLs plugin or a database search-and-replace with WP-CLI handles this.
Update canonical tags. If your pages have canonical tags (they should), ensure they reference the HTTPS version of each URL.
Update Google Search Console and Analytics. Google Search Console treats http:// and https:// as separate properties. Add and verify the HTTPS version of your site. Also update any Google Analytics, Google Ads, or other marketing tool configurations to reference HTTPS URLs, so conversion tracking and attribution continue to work correctly.
Consider HSTS. HTTP Strict Transport Security (HSTS) is a response header that tells browsers: "Always use HTTPS for this domain, even if someone requests HTTP." Once a browser has seen this header for your site, it will never attempt an HTTP connection — removing the brief window of vulnerability during the initial redirect. Enable HSTS through your server configuration or hosting settings once your HTTPS implementation is solid and you're confident in the redirect setup.
Common SSL Certificate Problems and How to Fix Them
Certificate expired. SSL certificates have expiration dates — typically 1 year for commercial certificates, 90 days for Let's Encrypt (though auto-renewal handles this). An expired certificate causes browsers to show a full security error page to visitors. Solution: renew the certificate, or set up automatic renewal if you're on Let's Encrypt. Monitor expiration dates for any certificates you manage manually.
Certificate doesn't match the domain. A certificate issued for yoursite.com won't cover www.yoursite.com unless it was specifically issued to cover both (modern certificates typically cover both, but verify). It also won't cover subdomains unless it's a wildcard certificate. Mismatched domain errors trigger browser warnings. Solution: obtain the correct certificate that covers the exact domains and subdomains your site uses.
Self-signed certificate. A certificate you generate yourself rather than obtaining from a trusted CA is not trusted by browsers. Visitors see a full security warning. Self-signed certificates are appropriate only for internal/development use, never for public-facing sites. Solution: replace with a certificate from Let's Encrypt or a commercial CA.
Certificate chain incomplete. TLS certificates use a chain of trust: your certificate, an intermediate certificate, and a root certificate. If your server isn't providing the complete chain to browsers, some browsers (particularly older mobile browsers) may show errors. Solution: configure your server to send the complete certificate chain, including intermediate certificates. Your CA should provide the necessary chain files.
Mixed content. Covered above — HTTP resources loading on an HTTPS page. Tools like Why No Padlock (whynopadlock.com) help identify exactly which resources are causing mixed content issues on any given page.
The Business Case in One Paragraph
An SSL certificate is no longer optional for any website that wants to be taken seriously. Browsers actively warn users about HTTP sites. Google ranks HTTPS sites above HTTP equivalents. Visitors who see security warnings leave immediately — before reading a word of your content. And the barrier to having HTTPS is essentially zero: free certificates exist, most platforms install them automatically, and setup takes minutes when it requires any manual work at all. There is no legitimate reason for a business website to be running without it in 2026.
The Bottom Line
SSL certificates enable the encrypted, authenticated connections that HTTPS provides. For most websites, a free DV certificate from Let's Encrypt is the right choice — full encryption, trusted by all browsers, automatically renewed. Managed platforms handle this entirely for you. Custom server setups take under 30 minutes to implement with Certbot. The certificate alone isn't enough — proper redirects, mixed content fixes, and HSTS complete the implementation.
Get this right from the start. If your site is still running on HTTP, fix it today. The cost is zero, the technical effort is minimal, and the downside of not doing it — browser warnings actively deterring your visitors — is both real and avoidable.
Every website built with Scalify launches with HTTPS properly configured, redirects in place, and all the foundational security and performance elements correctly implemented. The technical basics, handled right.







.jpeg)
.jpeg)